‘We kill people based on metadata‘- General Michael Hayden (former Director of the CIA & NSA) (1)
Introduction
We won’t pretend the quote above isn’t set at the top of the article intentionally to get your attention (but we hope it worked!). Metadata as a term doesn’t sound very exciting so we wanted to get your attention so as to not skip over this article. We hope you bare the quote in mind because as you’ll see metadata has many positive, important, and unavoidable uses in our daily lives which will make the quote even more disconcerting. We’ve also created and linked to a How-To Guide on removing metadata at the end of the article.
What is Metadata?
The simplest and most widely accepted definitions of metadata include ‘data about data’ or ‘data that describes data’. Both of which are correct technically but when it comes to a definition, they do very little to help understand or mentally imagine metadata, so let’s dig a little deeper.
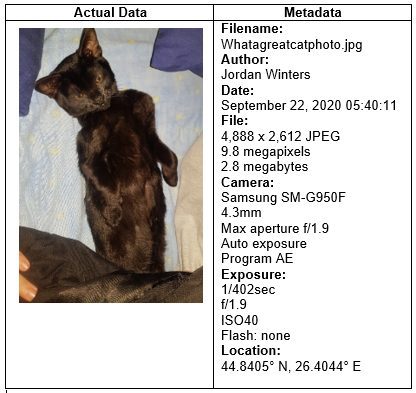
Metadata is not the actual data itself, the data itself being a photo, a document, a website, contents of an email, a video, and basically any file or information that can be found electronically. Metadata is bits of information that summarise or describe the actual data to make it easier to find such as the author, date created, file size, file type, location, device it was created on and so forth. The purpose of metadata is to make the actual data it belongs to easier to work with or find (usually both). For the mature readers, think of metadata as the card file in your high school library that contains information about a book or article. Here is an illustration of actual data and its associated metadata:
Another good way to imagine metadata is if you receive an envelope addressed to someone else by mistake. You cannot see the contents of the envelope of course however you can make some very educated decisions about it based on ‘metadata’. The size, weight, and colour of the envelope can reveal if the contents may be of a personal or business nature. You will obviously see the names (and possibly titles) with the addresses of both the sender and the receiver of the envelope hinting at their status. The postage stamp can reveal the location it was sent from and the date may be stamped over it telling you when it was processed. Whether the addresses on both sides are handwritten or printed can indicate likelihood of the contents being a personal message or mass distribution from a company database and so forth. This metadata therefore helps you reach a conclusion about the data contained within – that it is not information for you and prompt you to take appropriate steps (return to sender, ask your neighbours if it’s for them etc).
The positive uses of Metadata
This section is designed to illustrate to how metadata is used in our daily lives for a more wholesome understanding following the definition earlier. This section is intentionally broad and brief as we are going to focus on privacy concerns in the section to follow which is where we believe the detail is deserved and more relevant to the interests of our readers.
Websites
Metadata is critical in the success and visibility of a website from the perspective of the website being able to be found by a search engine. It’s also important to help anyone viewing a search engine result in identifying which website is more likely to be relevant to what they’re searching for.
Computer files
Every type of file you save on your device comes with its own metadata to help you find it later. If you’ve ever searched for a file on your computer you know you can filter your search using file type, date, size and other metadata of that file.
Social media
Metadata helps you identify potential friends or networks on various social media platforms from Facebook to LinkedIn. A search of location and job title for example will draw upon metadata to serve you the most relevant links toward the person you’re looking for.
Databasing
Similar to online searching of websites, metadata helps track down a certain document or article located within a database of millions. If you know some identifying features such as author, date or subject (which are all metadata) you should be able to find the document you’re looking for relatively quickly.
In simple terms the way we catalogue, store, search, and identify various files, media, people, or information in the digital age is made possible by metadata.
Metadata & your privacy
We alluded to metadata in our article Challenging the way you imagine Data & Privacy which is worth a read after this one. Every time you interact on social media, complete an action on your smartphone, communicate over the internet, use a search engine, amongst other similar activities, metadata is being created about you and your interaction whilst being called upon to help you complete certain actions as well.
Furthermore, online shopping sites and retailers can also use metadata to track your habits and preferences, every engagement on their digital assets can allow for this. These digital assets are things like their website, social media posts, apps, marketing emails (EDMs) which can all create metadata. Metadata can be on a range of metrics such as how long you spent on that page, what you clicked on, what time you opened it, how far down the sales funnel you went and much more. From there they know when the best time to serve you more posts, emails or other advertising based on when you’re most engaged and likely to spend.
Tracking by way of metadata doesn’t just extend to your favourite clothing store, Governments can (and some do) mandate metadata retention from national Internet Service Providers or Telecommunications Providers to store metadata on their citizens. This allows for government harvesting of metadata on what you do online, who you communicate with, when, which email providers you use etc. In democratic countries these metadata logging laws tend to be justified as a fight against law breaking activities or groups.
To keep things in perspective, remember metadata is not the data itself, it is descriptive or indicative of the data or simply a footprint of the data. This is of course still not ideal for the privacy conscious; however, it could be worse, below is what metadata can be created based on a couple of common activities most of us would perform on a daily basis:
Mobile phone call
The phone number of both parties, serial number (USI) of both phones, location of both parties (including directional movement if in transit), phone number of both parties, date & time of the call, duration the call lasted and more. However, the conversation itself is not saved or recorded nor forms part of metadata in any way.
Using Email
The name and email address of both parties, IP address of the sender, subject line of the email, number of attachments, login records of mail client used and more. However, the contents of the email is not saved or recorded as metadata in any way.
It’s quite disconcerting how such basic actions by today’s standards can reveal so much about an individual and their networks. If this was where the story ended some readers might accept it with a degree of acquiescence and think ‘well at least the contents of my interactions aren’t revealed‘. However, we have that quote to return to, let’s give it some more context.
The quote is actually in response to another equally eye opening quote by former NSA General Counsel Stewart Baker:
‘Metadata absolutely tells you everything about somebody’s life. If you have enough metadata, you don’t really need content‘ – Stewart Baker (former NSA General Counsel) (2)
This was posed to Michael Hayden who responded that it was ‘absolutely correct‘ and went the step further to make that statement ‘we kill people based on metadata‘. This refers to the strategy of the NSA to use metadata analysis and mobile phone tracking as the primary identification method of targets for drone strikes (as opposed to traditional intelligence). Read this article by The Intercept for more information on that program but fundamentally the issue was a lack of integrity and authenticity of the metadata. Aware of this program the bad actors (Taliban leaders in this case) swapped phones, used multiple phones, shared them between family and friends, and other methods to attempt to confuse the NSA analysts of the metadata. The result was, allegedly, a number of innocent people were incorrectly targeted and lost their lives.
People who are privacy conscious tend to be concerned about the content of their communications being compromised or otherwise not secured. The concern is more about what’s written in the email, the text message, or what’s said over the phone. However, we can see that metadata can be potentially more valuable than the actual data itself in terms of painting a picture about a person or their network. From a technical standpoint analysis of metadata is far easier and far quicker than analysis of data since the latter involves reading emails, listening to phone calls, etc. Finally, gaining access to metadata is much easier than gaining access to data in most jurisdictions around the world.
Metadata is a threat to good-natured, law-abiding, moral citizens in that it can reveal details about calls to, visits at, or associations with:
- Psychiatrists and other mental health care
- Medical specialists such as abortion clinics, sexual health clinics, and other private matters such as assistance programs for problem gambling, smoking or alcohol addiction.
- Legal but divisive businesses such as brothels and gun stores
- Whistle-blowers of illegal corporate activity can be undermined by the metadata of the photos they take or documents they leak, for example, as can journalists or political dissidents relying on anonymity.
The association to any of those listed above, usually coupled with other metadata for vindication (such as online searches) is enough to build a profile on a person with a high level of certainty without accessing the contents of any conversation or interaction with those places directly. This is simply a more relevant way of highlighting the same point as the NSA drone strike program earlier but in the context of how metadata can affect you personally and negatively.
The obvious place this leads to of course is bad actors online who may use acquired metadata against you for blackmail, ransom, or doxing. However, don’t forget about some of the points we discussed in The less obvious ways bad actors can access your data. You may be unaware of who has it in for you and in the future metadata could be used against you in family court when fighting for custody of your children, for example.
Another example of how it can be used against you or undermine your privacy (and even security!) is if you share photos with a new love interest by sending some selfies via SMS. If that relationship was to sour, especially early on, that person can access the metadata from those photos which may identify where you work or live amongst other bits of sensitive information. Our How-To Guide linked in the next section can help you alleviate these risks.
It goes without saying that law enforcement can also use metadata in an investigation or to track your whereabouts, such as proving or disproving an alibi for example. This can be beneficial if you are wrongfully accused however it’s likely that metadata alone won’t be strong enough to make or break a case.
How to control Metadata
Bad actors, governments and their various law enforcement agencies, and marketers are all chasing your metadata. However, there is little transparency and a legitimate lack of governance regarding the access and use of metadata. This has been aptly described as ‘authority creep’ whereby access to metadata records is by greater parties than intended. The list below relates to preventing metadata generation or deleting metadata and is relevant to online interactions, communication, or file storage and document management.
1 VPN: Using a VPN means the only metadata collected will be that the receiver’s data came from a certain VPN server. Ensure you use a no-logs provider of course.
2 Tor: Tor is the onion router which protects the anonymity of users and conceals internet activity from surveillance actors.
3. Use encrypted communication providers such as ProtonMail for email (amongst others) between all parties and Signal for messaging. We have listed some of the most highly rated of these at the end of our Encryption 101 article linked here. When choosing any security focused option such as these, it’s best practise to ensure their server isn’t in a Five Eyes country.
4. Remove EXIF data from photos especially if you share them digitally. The cat picture illustrated at start of this article showed the metadata attached to the photo which is stored as Exchangeable Image File Format (EXIF) data. Keeping this functionality turned on can provide metadata regarding the date, time, location, and the device a photo was taken on. See our How To Guide linked at the end of this section for help with removing and / or disabling metadata such as EXIF data from photos.
5. Remember each time you create an editable or shared file such as a spreadsheet or word processing document metadata is created within the file which may be of a sensitive or privileged nature. If you deal with legal contracts of any sort read this great article by Priori on the matter of metadata in documents but our How-To Guide covers this as well.
6. Finally, our How-To Guide on how to remove metadata from various file types across various devices and operating systems is linked here:
How-To Guide: How to remove metadata
Conclusion
We opened the article with the positive and necessary uses metadata has in helping us find the information we need in an increasingly digitised world. From finding a photo of your cat to potentially life saving information when time is of the essence – metadata is the enabler. We also saw the opposite; we also saw how metadata can be used against you both intentionally or as a result of poor-quality metadata analysis and decision making.
The biggest take away from this article is to highlight there is so much behind the scenes data (metadata) being created far beyond what most people realise. Be aware that metadata exists and if you feel it could be a threat to any legal activity you do, especially in a highly competitive business sector, take steps to ensure it is deleted or cannot be created in the first place.
References
Quote (1) by Michael Hayden
Quote (2) by Stewart Baker
Further reading & links used:
The Wikipedia article for Metadata is a great starting point for anyone who is interested about metadata more broadly (we focused on privacy concerns obviously)
The Priori article about metadata in shared documents
NSA use of Metadata to identify drone targets
Alleged misuse of metadata by the NSA
Article relating to quotes (1) & (2) by David Cole
Metadata & Authority Creep
Poor governance and oversight of access to metadata
This article is written in line with our Terms & Conditions and Disclaimer. As such all content is of a general nature only and is not intended as legal, financial, social or professional advice of any sort. Actions, decisions, investments or changes to device settings or personal behaviour as a result of this content is at the users own risk. Privacy Rightfully makes no guarantees of the accuracy, results or outcomes of the content and does not represent the content to be a full and complete solution to any issue discussed. Privacy Rightfully will not be held liable for any actions taken by a user/s as a result of this content. Please consider your own circumstances, conduct further research, assess all risks and engage professional advice where possible.

